Most Common IaaS Security Issues and Ways To Mitigate Them

Audio : Listen to This Blog.
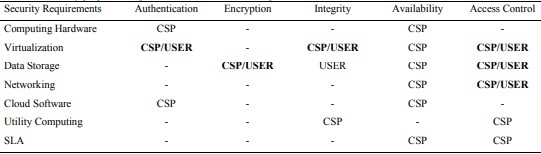
With today’s world of constant digitization, enterprises are continuously shifting their workload to the IaaS platform from the legacy infrastructure because of its speed and flexibility. Gartner expects IaaS to grow by nearly 13.4% to $50.4 billion by the start of 2021. However, as it is a cloud-driven concept, one cannot deny the presence of issues and security risks. The catch here is that just a single feature cannot provide complete security for the IaaS environment. It is so because the IaaS platform’s protection is a kind of shared responsibility, where customer security responsibilities involve ensuring cloud infrastructure is architected, deployed, and operated safely. The responsibilities also include maintaining the cloud security in aspects of firewalls, operating systems, data, platforms, etc. Whereas the providers have to secure the cloud in aspects like storage, global infrastructure, database, compute, etc.
IaaS security issues are the most critical concerns for both users and providers alike, which need to be solved for high performance. Therefore, we present this blog to make the readers aware of the IaaS security issues. This will help in choosing a suitable solution for business data protection.
Security issues in Infrastructure as a Service
Infrastructure as a Service has some issues that must be resolved for high performance. These issues can be divided into two broader categories.
Component wise security issues
1. Service level agreement or SLA driven issues:
SLA is the agreement between the client and the service provider concerning the quality of services and uptime guarantee. Enforcing the SLA and properly monitoring the SLA is one of the most common challenges one faces while maintaining trust between the provider and the client. The solution to this challenge is a Web Service Level Agreement (WSLA) framework, which is created to monitor and enforce the Service Oriented Architecture. WSLA maintains SLA trust by enabling third-party innovation to maintain the SLA provisions in cloud computing.
2. Utility computing driven issues:
Utility computing is known to be the commercial face of Grid and cluster computing, for which the users are charged per usage of services. The primary challenge involved with utility computing is its complexity; for instance, a service provider provides services to a 2nd provider, who also provides services to others. This makes it difficult to meter the services for the charges. The other challenging issue is that the whole system will become vulnerable to attackers who want to access services without paying. The answer to the first challenge is Amazon Devpay, which enables the provider at the 2nd level to meter the service usage and bill the consumer accordingly. The solution for the second challenge is that the service provider must keep the system clean from viruses and malware and keep the system risk-free. The system is also affected by the client’s practice; therefore, the client must keep the authentication keys safe.
3. Cloud software-driven issues:
Cloud software is the key that connects the cloud components to act as one single component. A cyber attacker has the power to attack against the XML services security protocols and attack the web services that can lead to a complete breakdown of the communication of services. The solution to mitigate these kinds of attacks is the XML signature for authentication and integrity protection. Another solution is XML Encryption that wraps the data in an encrypted manner, and that data needs to be decrypted to retrieve the original data.
4. Networks driven issues:
Internet connectivity and networking services play a critical role in delivering a service over the internet. There are issues in networks and internet connectivity, such as the “Man in the middle attack” – when an attacker manipulates the network connectivity by generating middle man access, from where the attacker can access all the classified permissions and data. The other type of such attack is known as the “flooding attack,” when an unauthorized user sends bulk requests to increase the chances of an attack due to those requests. The potential solutions can be like traffic encryption, which uses point-to-point protocols to encrypt the connectivity for avoiding the externals attacks. Another suitable solution can be continuous and efficient network monitoring on services to verify whether all networking parameters are running correctly or not. The externals attacks can also be avoided by implementing firewalls to protect the connectivity from outer attacks.
Overall security issues
Overall security issues are judged on the basis of overall services rented by an IaaS provider. A few of these type of issues are as follows:
1. Monitoring of data leakage and usage:
All the data that is stored in the cloud must be kept confidential. It indicates that the providers and the clients must be aware of how the data is being accessed and ensure that only authorized users have access to the data. These issues can be solved by up-to-date data management services, which will continuously monitor the data usage and also restrict the usages as per security policies.
2. Logging and reporting:
Proper logging and reporting modules must be employed effectively to make the deployment of IaaS more efficient. Superior logging and reporting solutions can keep track of the whereabouts of the information, its user, the information about the machines handling it, and the storage area keeping it.
3. Authorization and authentication:
It is a well-known fact that just using a user name and password may not be enough for a highly secure authentication mechanism. It is the most common security measure a system has to maintain. A service provider must use multi-factor authentication to tackle this threat.
Conclusion
These are some of the risks and issues that must be resolved before deploying any service in the cloud. Superior monitoring of the resources must be done effectively to accomplish the quality of services and high performance from the providers. It is always better to enforce preventive measures before the matter goes out of hand. Industry authorities strongly recommended taking IaaS security as a serious concern. Although securing an IaaS environment is a challenge, the high level of control enables a customer to design and implement the security controls as per their requirements.
